Efficient ring signature for cross-chain data sharing in blockchain-enabled cold-chain logistics system
Correctness
The signature \((e,c)\) should satisfy three conditions. First is\(\left\| e \right\|< e \right\\), as \(\left\\) is defined in the Ring Verify algorithm. Second is \( e \right\, as this condition is restricted system security reason. Third is \(c \leftarrow H({A_k}e+qcmod2q,\mu )\), as that it is based on the following Eq. (1) holds.
$$\begin{gathered} {A_k}e+qc={A_k}(A_{k}^{{ – 1}}(\sum\limits_{{i=1}}^{l} {{A_i}} ){y_1}+{y_2}+{( – 1)^b}{S_k}c)+qc \hfill \\ \quad \quad \quad \quad \;=(\sum\limits_{{i=1}}^{l} {{A_i}} ){y_1}+{A_k}{y_2}+{( – 1)^b}{A_k}{S_k}c+qc \hfill \\ \quad \quad \quad \quad \;=(\sum\limits_{{i=1}}^{l} {{A_i}} ){y_1}+{A_k}{y_2}+{( – 1)^b}qc+qc \hfill \\ \quad \quad \quad \quad \;=(\sum\limits_{{i=1}}^{l} {{A_i}} ){y_1}+{A_k}{y_2}\bmod 2q \hfill \\ \end{gathered}$$
(1)
Security proof
Security proof of the anonymity and unforgeability have been given in the following two subsections.
Anonymity
For the RS’s anonymity, the case of full key exposure should be taken into consideration, and detailed proof processes are shown in the following.
Theorem 1
Based on the hardness of lattice assumption \(\Re – SIS_{{q,n,m,\beta }}^{\kappa }\), this RS can achieve anonymity under full key exposure.
Proof
Suppose there exists an adaptive adversary A, who performs attack on the RS’s anonymity under full key exposure. Then, there exists a challenger who can execute a query-respond game with A to solve SIS problem a polynomial time algorithm C.
First and foremost, parameters \(n,m,q,\kappa ,\sigma\) are given. C performs the Key Gen. with \({q_E}\) times to derive ring group members’ public keys \({A_i} \in {\mathbb{Z}}_{{2q}}^{{n*m}},\;(i=1,2,…,l)\) and the corresponding secret keys \({S_i} \in {\mathbb{Z}}_{{2q}}^{{m*n}}\). Here, \({R_i}=\{ 1,2,…,{q_E}\}\)is the ring of these \({q_E}\) members. C initializes an empty list \(lis{t_K}\)storing \(\left\langle {i,{A_i},{S_i}} \right\rangle\), and then sends the public key set \(\{ {A_1},{A_2}, \ldots ,{A_l}\}\) to A.
Hquery: C initializes an empty list \(lis{t_H}\)storing \(\left\langle {{R_i},{u_j},{c_{ij}}} \right\rangle\). Upon receiving a Hquery from A, C first checks the query history. If this query already exists, C finds the storing \(\left\langle {{R_i},{u_j},{c_{ij}}} \right\rangle\) on \(lis{t_H}\) and returns \({c_{ij}}\) back. Otherwise, he randomly selects \({y_1},{y_2} \leftarrow D_{\sigma }^{m}\) at random and computes \({c_{ij}} \leftarrow H((\sum\limits_{{i=1}}^{l} {{A_i}} ){y_1}+{A_k}{y_2}mod2q,{\mu _j})\). Then, he adds \({c_{ij}}\) to \(lis{t_H}\), and returns it to A.
Private key query
For member \({i_1}’s\) private key query, C checks list \(lis{t_K}\) and returns \({S_i}\) back to A.
Sign query
For member \({i_1}’s\)sign query on signature \(\left\langle {k,{R_i},{u_j},{e_{ij}}} \right\rangle\), C first checks the query history. If this query already exists, C finds the storing \(\left\langle {{i_1},{R_i},{u_j},{e_{ij}}} \right\rangle\) on \(lis{t_S}\) and returns \({e_{ij}}\) back. Otherwise, C first performs H query to obtain \({c_{ij}}\), and randomly selects \(b \in \{ 0,1\}\) to compute the signature \({e_{ij}}\) by \({e_{ij}} \leftarrow A_{{{i_1}}}^{{ – 1}}(\sum\limits_{{i=1}}^{l} {{A_i}} ){y_1}+{y_2}+{( – 1)^b}{S_{{i_1}}}c\). Then, he adds \(({e_{ij}},{c_{ij}})\) to \(lis{t_S}\), returns it back to A.
Forge phase: A launches a challenge \(\left\langle {{k_0},{k_1},{R^*},{u^*}} \right\rangle\), where ring \({R^*}\) signs on the target message \({u^*}\). \({k_0}\) and \({k_1}\) are two members of ring \({R^*}\). C chooses \({t^*} \in \{ 0,1\}\), checks the \(\left\langle {{R^*},{u^*},{c^*}} \right\rangle\) in list \(lis{t_H}\), and derives the associated secret “trapdoor” \({S_{{R^*}}}\) with relation to \({A_{{R^*}}}\). Then, he computes a challenge signature \({e_{ij}}\), and returns it to A. Next, A gives his guess \(t^{\prime} \in \{ 0,1\}\).
It can easily derive that the statistical distance of \({e_{{k_0}}}’s,{e_{{k_1}}}’s\) distribution and \(D_{\sigma }^{m}\) is negligible. Therefore, the statistical distance of \({e_{{k_0}}}\) and \({e_{{k_1}}}\) is also negligible. This derives that A guesses 0 or 1 with the same probability. So, the proposed RS scheme has anonymity under full key exposure.
Unforgeability
For the RS’s unforgeability, the case of insider attack should be taken into consideration.
Theorem 2
Based on the hardness of lattice assumption \(\Re – SIS_{{q,n,m,\beta }}^{\kappa }\), this RS can achieve unforgeability under insider attack.
Proof
Assume there exists an adaptive adversary A, who performs attack on the RS’s unforgeability under insider attack. Then, there exists a challenger who can execute a query-respond game with A to solve SIS problem by a polynomial time algorithm C.
First and foremost, parameters \(n,m,q,\kappa ,\sigma\) are given. C selects \(l \in \left[ {{q_E}} \right]\) as the number of challenge ring member. He obtains a SIS instance \({A_{{R_t}}} \in Z_{q}^{{n \times lm}}\) and divides this \(n \times lm\) matrix into l matrixes with \(n \times m\). Note that \({A_{{R_t}}}=[{A_{1*}}{A_{2*}} \cdots {A_{l*}}]\), where \({A_{{i^{st}}}} \in Z_{q}^{{n \times m}}\). C selects \({t_i} \in \left[ {{q_E}} \right],i \in \{ 1,2, \cdots ,l\}\), and sets \({R_t}=\{ {t_1},{t_2}, \cdots ,{t_l}\}\). Then, C servers the sub-matrix \({A_{i*}}\) as the public key of ring \({R_t}\) member. Therefore, \({A_{ti}}={A_{i*}}\) for the member in ring \({R_t}\). For the \({q_E} – l\) ring member out of \({R_t}\), C performs the Key Gen. with \({q_E}\) times to derive ring group members’ public keys \({A_i} \in {\mathbb{Z}}_{{2q}}^{{n*m}},\;(i=1,2,…,l)\) and the corresponding secret keys \({S_i} \in {\mathbb{Z}}_{{2q}}^{{m*n}}\). Here, \(R=\{ 1,2,…,{q_E}\}\)is the ring of these \({q_E}\) members. C initializes an empty list \(lis{t_K}\)storing \(\left\langle {i,{A_i},{S_i}} \right\rangle\), and then sends the public key set \(\{ {A_1},{A_2}, \ldots ,{A_{{q_E}}}\}\) to A.
Hquery: C initializes an empty list \(lis{t_H}\)storing \(\left\langle {{R_i},{u_j},{c_{ij}}} \right\rangle\). Upon receiving a Hquery from A, C first checks the query history. If this query already exists, C finds the storing \(\left\langle {{R_i},{u_j},{c_{ij}}} \right\rangle\) on \(lis{t_H}\) and returns \({c_{ij}}\) back. Otherwise, he randomly selects \({y_1},{y_2} \leftarrow D_{\sigma }^{m}\) at random and computes \({c_{ij}} \leftarrow H((\sum\limits_{{i=1}}^{l} {{A_i}} ){y_1}+{A_k}{y_2}mod2q,{\mu _j})\). Then, he adds \({c_{ij}}\) to \(lis{t_H}\), and returns it to A.
Private key query
For member \({i_1} \notin {R_t}\) private key query, C checks list \(lis{t_K}\) for \(\left\langle {{i_1},{A_{{i_1}}},{S_{{i_1}}}} \right\rangle\) and returns \({S_i}\) back to A. Otherwise, abort.
Sign query
For member \({i_1}’s\)sign query on signature \(\left\langle {{i_1},{R_i},{u_j},{e_{ij}}} \right\rangle\), there exist three cases which should be taken into consideration.
Case 1
If \({R_i}={R_t}\), C first checks the query history. If this query already exists, C finds the storing \(\left\langle {{i_1},{R_i},{u_j},{e_{ij}}} \right\rangle\) on \(lis{t_S}\) and returns \({e_{ij}}\) back. Otherwise, C first performs Hquery to obtain \({c_{ij}}\), and randomly selects \(b \in \{ 0,1\}\) to compute the signature \({e_{ij}}\) by \({e_i} \leftarrow A_{k}^{{ – 1}}(\sum\limits_{{i=1}}^{l} {{A_i}} ){y_1}+{y_2}+{( – 1)^b}{S_k}c\). Then, he adds \(({e_i},{c_{ij}})\) to \(lis{t_S}\), returns it back to A.
Case 2
If \({R_i} \ne {R_t}\) and \({i_1} \in {R_i} – {R_t}\), the \(\left\langle {{i_1},{A_{{i_1}}},{S_{{i_1}}}} \right\rangle\) exists in list \(lis{t_K}\). C first checks the query history. If this query already exists, C finds the storing \(\left\langle {{i_1},{R_i},{u_j},{e_{ij}}} \right\rangle\) on \(lis{t_S}\) and returns \({e_{ij}}\) back. Otherwise, C first performs Hquery to obtain \({c_{ij}}\). Then, he derives the associated secret “trapdoor” \({S_{{R_i}}}\) with relation to \({A_{{R_i}}}\), and randomly selects \(b \in \{ 0,1\}\) to compute the signature \({e_{ij}}\) by \({e_{ij}} \leftarrow A_{{{R_i}}}^{{ – 1}}(\sum\limits_{{i=1}}^{l} {{A_i}} ){y_1}+{y_2}+{( – 1)^b}{S_{{R_i}}}{c_{ij}}\). Then, he adds \(({e_i},{c_{ij}})\) to \(lis{t_S}\), returns it back to A.
Case 3
If \({R_i} \ne {R_t}\) and \({i_1} \in {R_i} \cap {R_t}\), the \(\left\langle {{i_1},{A_{{i_1}}},{S_{{i_1}}}} \right\rangle\) does not exist in list \(lis{t_K}\). C first checks the query history. If this query already exists, C finds the storing \(\left\langle {{i_1},{R_i},{u_j},{e_{ij}}} \right\rangle\) on \(lis{t_S}\) and returns \({e_{ij}}\) back. Otherwise, C first finds a \({i_2} \in {R_i} \cap {R_t}\) as the \(\left\langle {{i_2},{A_{{i_2}}},{S_{{i_2}}}} \right\rangle\) exists in list \(lis{t_K}\). Then, he derives the associated secret “trapdoor” \({S_{{R_i}}}\) with relation to \({A_{{R_i}}}\), performs H query to obtain \({c_{ij}}\), and randomly selects \(b \in \{ 0,1\}\) to compute the signature \({e_{ij}}\) by \({e_{ij}} \leftarrow A_{{{R_i}}}^{{ – 1}}(\sum\limits_{{i=1}}^{l} {{A_i}} ){y_1}+{y_2}+{( – 1)^b}{S_{{R_i}}}{c_{ij}}\). Then, he adds \(({e_{ij}},{c_{ij}})\) to \(lis{t_S}\), returns it back to A.
Suppose ε represents the probability that A outputs a legitimate signature. Here, the probability that C successfully solve the SIS instance is mainly depended on the private key query phase and challenge phase. As there are l ring member in R, the probability of successfully private key query for \(i \notin {R_t}\) is \(1 – 1/{q_E}\), and the probability of successfully challenge for \({R^*}={R_t}\) is \(1/C_{{{q_E}}}^{l}\). Therefore, the probability that challenger C successfully solve the SIS instance is at least \(\varepsilon \left( {1 – 1/{q_E}} \right)/C_{{{q_E}}}^{l}\). Here, with the query times \({q_E}\) increasing, the success probability becomes more negligible. So, the proposed RS scheme has unforgeability under insider attack.
Undeniable
For this RS scheme, one ring member can represent the ring group to sign the message, and the ring group users cannot deny this signature. As in the signature generation process, all the public keys of ring members are constructed by \(\sum\limits_{{i=1}}^{l} {{A_i}}\). In the one hand, this mechanism guarantees that the signer is authorized by the ring group, and the ring signature is approved by all the ring group members. In the other hand, this construction provides a signature traceability mechanism as it can quickly find the target user once the medical disputes occur. This security property can protect the user privacy as it cannot know which member of the real signer is, and also provide a secure traceability mechanism for the cold-chain logistics data sharing in the BCCLS.
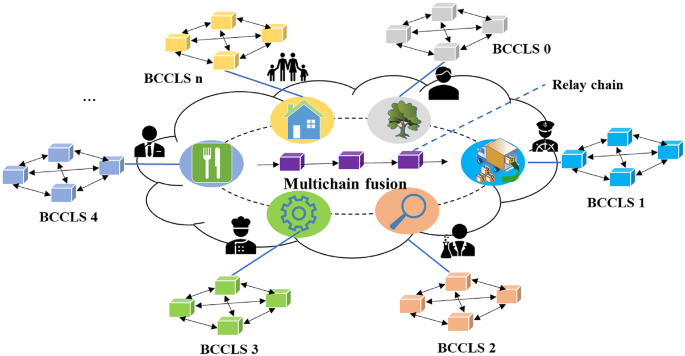
Therefore, the proposed RS scheme can satisfy the security properties of correctness, anonymity, unforgeability, and undeniable. This RS scheme supports the transaction ring signing model and establishes a ring signature mechanism for one cold-chain logistics product circulating in different institutions. In addition, this RS scheme improves the cross-chain transactions security with the multi-chain fusion mechanism in the BCCLS. The fusion ledger protects the immutability of the cold-chain logistics data and provides a mechanism for traceability of the cross-chain data processing.
link






